Systems leaders… are your Salesforce integrations creating some serious security risks? With departments like marketing, sales, and operations continuously tweaking and integrating new tools to Salesforce, it’s easy to lose track of who is making changes and where your data is going. Given that the average company uses over 1000 applications, many connected to Salesforce, this can quickly become a problem.
To help, we’re sharing three real-world examples of how Salesforce integrations could quickly turn into vulnerabilities for your business. And these aren’t just hypotheticals; they’re scenarios that could very likely be happening right now. By understanding these risks and working closely with your RevOps and go-to-market (GTM) teams, you can identify and mitigate these issues before they escalate.
Let’s dive in and make sure your Salesforce integrations are secure and serving your business, not threatening it.
3 Real-World Examples of How Your Salesforce Data Could Be At Risk
Without a doubt, you and your business systems team juggle a myriad of responsibilities, particularly around security. Keeping tabs on Salesforce integrations might feel like just another hefty task added to your ever-expanding list of systems to monitor. However, the ability to swiftly pinpoint potential risk alongside your Ops team is crucial. Below, we outline three common scenarios to watch for that could signal security risks emanating from your Org.
Scenario 1: Unauthorized Integration and Data Push by a Salesperson
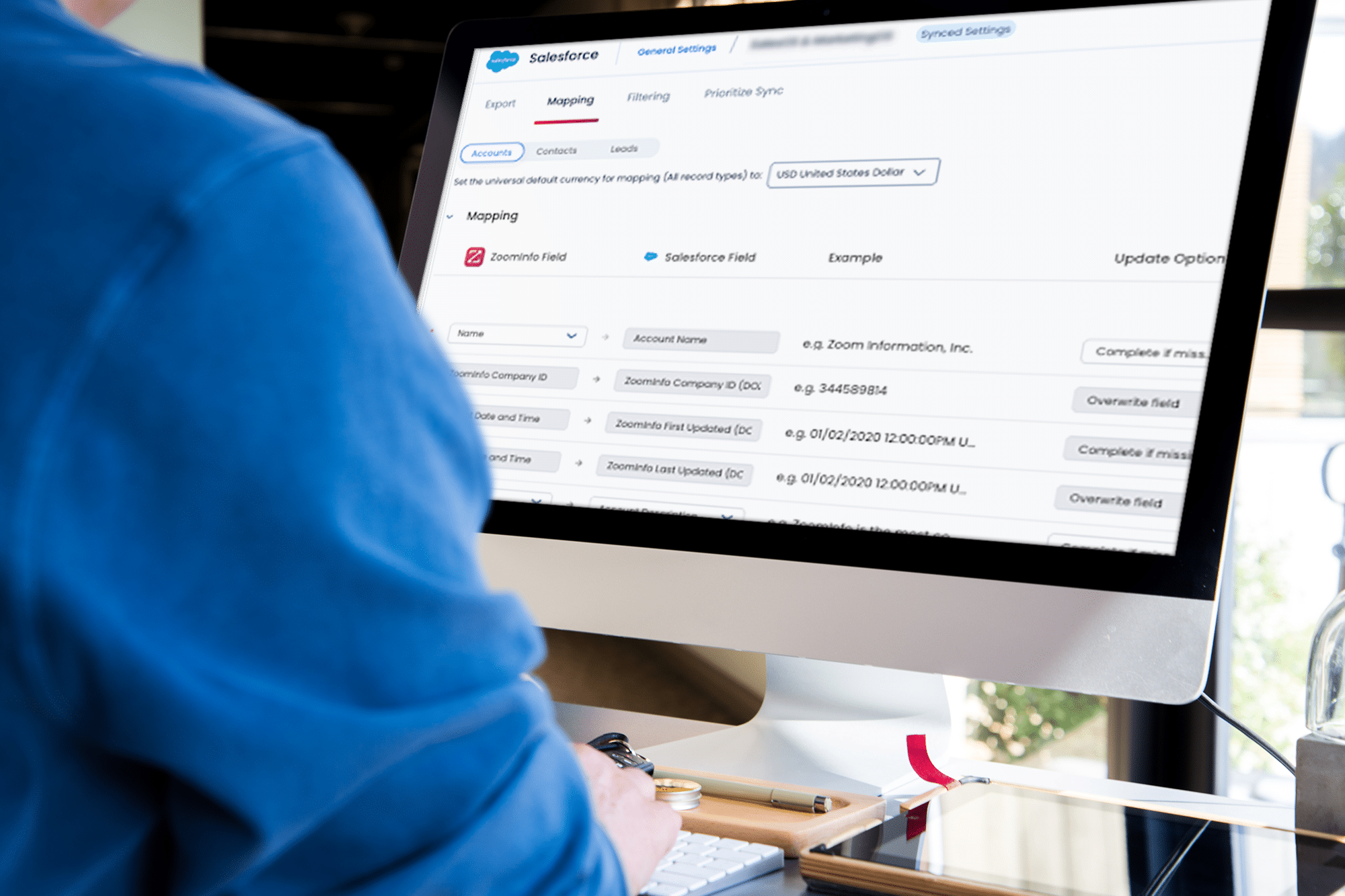
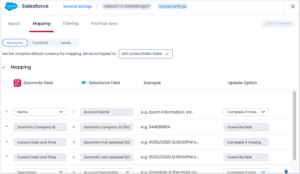
Here’s a common scenario. Consider a situation where a salesperson uses ZoomInfo to map EU emails into Salesloft and subsequently places those addresses into a marketing workflow. This action, while seemingly innocuous in pursuit of sales targets, breaches GDPR compliance.
The unauthorized use of personal data without explicit consent can lead to severe legal penalties and damage your organization’s reputation. This highlights a critical gap: without strict controls on who can integrate and push data to and from Salesforce, your organization risks non-compliance with international data protection regulations.
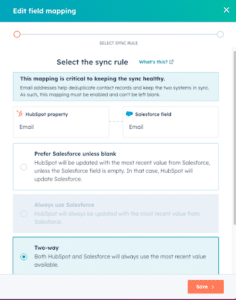
Scenario 2: Unrestricted Marketing Access to Field-Level Mapping from HubSpot
Here’s another one. While Marketing teams are vital for driving growth they can inadvertently become a source of data breaches without proper checks and balances in place. A very real and common scenario of this is when a marketer in HubSpot creates a new field and maps it to an existing sensitive field in Salesforce, like personal identifiers or financial information.
Oftentimes this can lead to overwriting critical data or inadvertently sharing sensitive information. Without restrictions and oversight on how data fields are mapped and modified, your Salesforce data integrity is at constant risk, opening the door to potential data mishandling and compliance issues.
Scenario 3: Unencrypted Patient Feedback Passed to Salesforce
Another example of potential security risk is if your customer success team uses a third-party platform to generate call recordings and transcriptions from patient interactions. If these transcriptions are not encrypted before syncing with Salesforce, personal health information (PHI) could be exposed. This scenario is particularly precarious for organizations under HIPAA regulations. Syncing unencrypted PII into Salesforce not only risks compliance fines but also exposes sensitive patient data, jeopardizing patient trust and your company’s credibility.
5 Signs Your Salesforce Integrations Are Creating Data Security Risk
Identifying potential security risks in Salesforce integrations is a proactive step that can save your organization from significant repercussions. But identifying the tell-tell signs of a potential threat can be difficult, especially when Salesforce hasn’t traditionally been part of your oversight. The key is working alongside your Ops team to ensure compliance.
Here are five ways to evaluate if your Salesforce integrations might be exposing you to security vulnerabilities.
1. Unexpected data entries and changes
Keep an eye on unusual entries or modifications in your Salesforce data. Unplanned or unrecognized changes can often signal unauthorized data manipulation or integration issues.
2. Audit trail anomalies
Regularly review the audit trails for activities related to data integration. Gaps or inconsistencies in these logs can indicate unsanctioned activities or shadow IT operations.
3. Compliance alerts
Stay alert for any compliance notifications or warnings from data protection tools. These can often flag activities like the unauthorized processing of PII or other sensitive information.
4. Surge in user access issues
An increase in access-related issues or permissions errors can be a telltale sign of over privileged accounts or poorly managed access controls.
5. Feedback from users
Direct feedback from users encountering data inconsistencies, or unauthorized data exposure can also be a crucial indicator of underlying security flaws.
How to Mitigate Salesforce Data Risks
If you suspect that your Salesforce integrations might be putting your organization at risk, it’s crucial to act sooner rather than navigate data loss later. Addressing vulnerabilities proactively can save you from the far greater challenge of managing data breaches and loss in the future. Here are several effective strategies to ensure your Salesforce environment is secure:
1. Conduct a comprehensive audit
If you suspect that your Salesforce integrations may be compromised, start with a thorough audit of all integrations and data flows. Look specifically for any unauthorized or unexpected connections.
2. Review and restrict access controls
Evaluate who has the ability to change or integrate data within Salesforce. Tighten access controls and ensure that only authorized personnel have the capabilities to make changes, especially for sensitive data fields.
3. Implement event monitoring
If you are in a highly compliant industry like healthcare or finance, Salesforce Shield might be a wise investment to help mitigate risk. Shield combined with advanced event monitoring tools provide deeper visibility into the activities within your Salesforce environment. It enables you to track detailed interactions, including logins, data exports, and changes to records or configurations.
4. Build a data loss prevention policy for Salesforce
Establish a robust data loss prevention (DLP) policy specifically tailored for your Salesforce environment. This policy should include guidelines on how data should be handled, who has access to what data, and the procedures for monitoring and preventing potential data leaks.
5. Educate and train staff
Mitigating risk should be a company-wide initiative. Regular training sessions for all staff members who interact with Salesforce are critical. Ensure they understand the importance of compliance and the dangers of shadow IT.
6. Develop a response plan
Have a clear incident response plan that outlines steps to take when a security breach or risk is detected. This should include containment strategies, stakeholder communication, and remediation processes.
7. Use encryption and secure data practices
Ensure that all data, especially sensitive or personally identifiable information, is encrypted when being transferred or stored. Adhering to best practices in data security can significantly reduce risks.
Conclusion: Safeguarding Your Salesforce Environment with Proactive Security Measures
While integrations can significantly enhance functionality and streamline workflows, they also introduce potential vulnerabilities that can compromise your Org’s data security. Don’t overlook the scenarios happening every day within your business. They’re likely gaps that can be improved on. The importance of being proactive rather than reactive in your security strategy cannot be overstated. By taking preventative measures such as conducting regular audits, enhancing monitoring capabilities, managing access controls, and ensuring continuous staff education, you can protect your organization against the ever-present threat of data breaches.
Of course, as your organization’s tech stack grows and evolves, so does the complexity of ensuring that every piece communicates effectively and securely. This is where Sonar steps in, providing a robust solution for proactive data loss prevention and integration management.
Sonar offers unparalleled visibility across your integrated tech stack, enabling Ops, Business Systems, and InfoSec teams to proactively manage risks and collaborate effectively. With its advanced monitoring tools and real-time alerts, Sonar ensures that sensitive data remains protected and integrations function smoothly. Try Sonar free today!